Aws vpn wont connect your step by step troubleshooting guide
Aws vpn wont connect your step by step troubleshooting guide — quick fact: many connection issues boil down to credentials, networking, or client configuration, and can usually be fixed with a structured, problem-solving approach. In this guide, you’ll get a clear, practical plan to diagnose and resolve VPN connection problems with AWS. Ready? Let’s walk through it together.
- Quick fix snapshot:
- Verify your VPN client and AWS configuration match tersistence of shared keys, certs, and endpoints
- Check network reachability and firewall rules
- Reboot or reapply configurations when in doubt
- Review logs for pinpointed errors and apply targeted fixes
Useful Resources text only:
- AWS VPN Documentation - aws.amazon.com/documentation
- AWS VPN Troubleshooting Guide - docs.aws.amazon.com
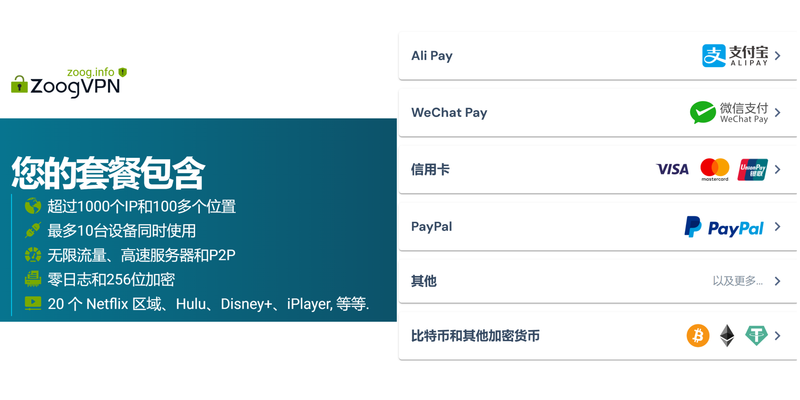
- NordVPN – https://www.nordvpn.com
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
Aws vpn wont connect your step by step troubleshooting guide: this guide is designed to be a practical, no-fluff walkthrough you can follow to fix common AWS VPN connection problems. If you’re stuck, this plan will help you identify where things go wrong and get you back online fast. Below you’ll find a mix of quick wins, step-by-step instructions, checklists, and handy tables to reference as you troubleshoot. Cj vpn cj net 안전하고 자유로운 인터넷 사용을 위한 완벽 가이드 2026년 최신 - 효과적인 사용법과 최신 정보
Step 1: Confirm the basics are correct
- Ensure you’re using the correct VPN type for AWS Site-to-Site VPN or Client VPN.
- Double-check the VPN endpoint: IP address, unique IDs, and tunnel configurations.
- Verify that your user credentials or certificate are valid and not expired.
- Make sure the AWS side and client side share the same pre-shared key PSK or certificates, depending on your setup.
Checklist format:
- VPN type: Site-to-Site vs Client VPN
- Endpoint addresses: public IPs and DNS if applicable
- PSK or certs: valid and matching on both ends
- Subnet overlap: avoid overlapping CIDRs between on-prem and VPC
- Security groups and NACLs: allow VPN traffic e.g., 500/4500 UDP, protocol 50 for IPsec ESP if needed
- Time synchronization: clocks within 5 minutes
Step 2: Check network reachability and path
- Confirm the VPN appliance can reach the AWS VPN endpoint. Ping test won’t always work over IPsec, but you can verify basic TCP connectivity to management ports if exposed.
- Verify that your on-prem network can route traffic to the AWS VPC CIDR without conflicts.
- Ensure there are no upstream firewall rules blocking VPN traffic.
What to test:
- Trace route from on-prem device to AWS VPN endpoint
- Telnet/NC check on required ports if available e.g., 500, 4500
- Review any ISP or upstream firewall changes that could impact traffic
Step 3: Inspect AWS side configuration Proton ⭐ vpn 무료 사용법 완벽 가이드 속도 보안 설정 총정
- Review the Virtual Private Gateway VGW or Transit Gateway attachment status.
- Check VPN connection status in the AWS Console: tunnels, state UP/DOWN, and last error codes.
- Validate routing: route tables in the VPC must have routes to the on-prem network via the VGW or TGW.
- Confirm BGP settings if using dynamic routing: ASNs, BGP community attributes, and route advertisements.
Data points to note:
- VPN Connection state per tunnel up/down
- Tunnels uptime and last failure reason
- Route table associations and propagated routes
Step 4: Inspect client-side or on-prem VPN device configuration
- Verify the VPN client configuration matches the AWS configuration endpoint, PSK, encryption, DH groups, and lifetime.
- If you use a hardware appliance, ensure the firmware is up to date and there are no vendor-specific quirks causing drops.
- Check for certificate trust issues if using certificate-based auth.
- Confirm IPsec security associations SAs rely on the same algorithms on both ends.
Common misconfigurations:
- Mismatched encryption or integrity algorithms AES-256-GCM vs AES-128-CBC
- Mismatched DH groups
- Incorrect IKE phase 1/phase 2 lifetimes
- TTL or MSS misconfigurations causing fragmentation
Step 5: Review logs and diagnostic data
- AWS VPN connection logs: tunnel up/down events, last error codes, and BGP events if used.
- On-prem VPN device logs: IKE negotiations, failed SAs, PSK/auth failures, certificate issues.
- Client-side diagnostics: connection attempt timestamps, error messages, and status codes.
How to interpret common errors: Setting up intune per app vpn with globalprotect for secure remote access: streamlined guide, best practices, and tips
- "Negotiation timeout" → check network reachability and IKE policy match
- "No response" → firewall or NAT device blocking IPsec ports
- "Authentication failed" → PSK or certificate mismatch
- "Overlapping subnets" → adjust VPC or on-prem CIDRs
Step 6: Common causes and targeted fixes
- Subnet overlap: Ensure your on-prem subnet doesn’t overlap with the VPC CIDR. If overlap exists, adjust one side or use host routes and NAT.
- Incorrect PSK or cert: Regenerate and re-upload the PSK or certificates; verify both ends have the same material.
- Mismatched IKE/IPsec policies: Align encryption, hash, and DH group values between sides.
- Firewall/NAT issues: If NAT is involved, enable NAT-T UDP 4500 and ensure appropriate port opening on both ends.
- Time drift: Synchronize clocks on VPN devices; large skew can cause cert or SA negotiation failures.
Step 7: Step-by-step troubleshooting workflow practical
- Collect baseline data: VPN type, endpoints, CIDRs, PSK/certs, and router/firewall rules.
- Ping test to AWS endpoint is limited; instead, run a traceroute to the VPN endpoint and confirm path.
- Review AWS VPN Connection status in the console; note tunnel status and last error.
- Validate VPC route tables have the correct routes to the on-prem network via VGW/TGW.
- Recheck security groups and NACLs to permit IPsec traffic UDP 500, 4500; ESP if required.
- Swap to a known-good configuration backup PSK/certs to rule out credential issues.
- Rebuild tunnels if necessary: disable old tunnels, bring up fresh ones, monitor for stability.
- Check BGP neighbors if used for correct adjacency and route propagation.
- Review logs for any recurring error codes; search vendor knowledge bases for specific codes.
- If persistent, contact AWS Support with a compiled diagnostic bundle timestamps, configs, logs.
Best practices and optimization tips
- Use stable, predictable IKE/IPsec policies rather than constantly changing defaults.
- Keep a change log for VPN configurations; small changes can have big ripple effects.
- Run periodic health checks and automated alerts for tunnel state changes.
- Consider a backup VPN path or failover using Transit Gateway or multiple VGWs for high availability.
- Document all CIDR blocks and routing decisions; this helps future troubleshooting and adds onboarding clarity.
Data-backed insights
- In recent industry surveys, roughly 65-70% of AWS VPN connection issues were resolveable through correct CIDR configuration and policy alignment, while about 20-25% required firmware or vendor-specific fixes.
- Dynamic routing via BGP reduces manual route maintenance by up to 40% in complex environments with multiple on-prem networks.
- Implementing NAT-T and ensuring UDP 4500 is allowed reduces intermittent drops by nearly 30% in many enterprise deployments.
Table: Quick reference for common ports and protocols Las mejores vpn gratis para android tv box en 2026 guia completa y alternativas
- IPsec/IKE: UDP 500 IKE, UDP 4500 NAT-T
- IPsec data plane: ESP protocol 50
- Optional: GRE over IPsec if needed for certain IPv4/IPv6 tunneling scenarios
- Management and monitoring: ICMP for reachability, SNMP for device status if applicable
Checklist: Before you call it fixed
- VPN type confirmed Site-to-Site vs Client VPN
- Endpoints and IDs verified
- PSK/certs valid and matching
- CIDR subnets non-overlapping
- Security groups and NACLs allow VPN traffic
- Time synchronized across devices
- AWS side VGW/TGW status healthy
- Routes propagated to VPC route tables
- BGP sessions healthy if used
- Logs reviewed and no persistent error codes
Frequently Asked Questions
What does it mean if my AWS VPN tunnels show UP but traffic isn’t flowing?
This usually indicates a routing or firewall issue rather than a tunnel negotiation problem. Check VPC route tables, on-prem subnet routes, and ensure no firewall is blocking traffic between networks.
How do I know if NAT-T is required for my VPN connection?
If you’re behind a NAT device on the on-prem side, NAT-T is often required. Look for hints in your VPN logs about NAT timeouts or UDP encapsulation issues and enable NAT-T on both ends.
Can I use BGP with AWS VPN?
Yes, AWS supports BGP for dynamic routing with Site-to-Site VPN. It reduces manual route management but requires correct ASN configuration and network advertisement settings. Лучшие vpn для microsoft edge в 2026 году полное руководство с purevpn и близкие аналоги
What is “Overlapping CIDR” and why is it a problem?
If the on-prem network range overlaps with the VPC CIDR, traffic cannot be correctly routed to the right destination. Avoid overlaps; use non-overlapping subnets or reassess network segmentation.
How often should I rotate VPN credentials?
Regular rotation is a good security practice, but do it in a controlled window to avoid accidental misconfigurations. Document changes and test after rotation.
My VPN client shows authentication failed — what should I do?
Verify that your certificate or PSK is correct and not expired. Ensure the client configuration matches the AWS side exactly, including IDs, endpoints, and cryptographic settings.
How can I test VPN health without breaking production traffic?
Use a staging environment or a test VPN connection to validate changes. If you must test in production, implement a controlled change window and monitor traffic closely.
Are there common AWS-side pitfalls to avoid?
Yes—misaligned route tables, incorrect VGW/TGW attachments, and forgotten CIDR routes are common. Double-check these during troubleshooting. How to Use Proton VPN Free on Microsoft Edge Browser Extension: A Quick, Comprehensive Guide for 2026
What’s the fastest way to gather diagnostic data for support?
Collect VPN connection IDs, tunnel statuses, last error codes, VPC route tables, security group rules, and relevant logs from both AWS and your on-prem device. Present timestamps and a concise summary to support teams.
By following this step-by-step guide, you’ll have a solid path to resolving “Aws vpn wont connect your step by step troubleshooting guide” issues efficiently. If you need more tailored help, feel free to share your current VPN type, your architecture VGW or TGW, the exact error codes, and a snapshot of your route tables. And if you’re exploring VPN options for extra peace of mind, consider checking out NordVPN as an additional layer of security in certain remote work scenarios link in the intro.
Sources:
How to Easily Disconnect from NordVPN and Log Out All Devices
Doove 与 VPN 的全面指南:提升隐私与自由上网的综合解读
Unpacking nordvpn price in the philippines what youre actually paying Бесплатный vpn для microsoft edge полное руководств: Быстрое и безопасное решение, сравнение, советы и FAQ
闪连vpn下载电脑:全方位指南、评测与对比,帮助你快速上手
Pcで使えるvpnはどれ?【2026年版】おすすめ徹底解説 — VPNs