Is Using a VPN Safe for Your IMAP Server Lets Break It Down
Is using a VPN safe for your IMAP server lets break it down. A quick fact: using a VPN to connect to your IMAP server can improve privacy and security, but it also introduces potential pitfalls if not configured correctly. In this guide, we’ll walk you through everything you need to know, from the basics of IMAP and VPNs to real-world setup tips, risks, and best practices. Think of this as a friendly, practical road map you can follow today.
- Quick start recap:
- VPNs can encrypt your email traffic between you and the IMAP server, shielding sensitive data from local networks.
- A poor VPN setup can cause connection drops, latency, or authentication issues.
- Always choose a reputable VPN provider with robust logging policies, strong encryption, and DNS leak protection.
Useful URLs and Resources text only, not clickable:
- VPN basics - en.wikipedia.org/wiki/Virtual_private_network
- IMAP protocol overview - en.wikipedia.org/wiki/Internet_Message_Archive_Protocol
- Email security best practices - csrc.nist.gov/publications/sp800-53
- TLS vs VPN for email - s
- NordVPN official page - nordvpn.com
- SSL/TLS best practices - tls13.ulfheim.net
Table of contents
- Why you’d want a VPN for IMAP
- How IMAP works and where VPN helps
- When a VPN can be risky for IMAP
- VPN features that matter for email
- Step-by-step setup guide
- Common pitfalls and troubleshooting
- Security best practices beyond VPN
- Real-world scenarios and decision tips
- FAQ
Why you’d want a VPN for IMAP
- Privacy in public or shared networks: If you’re on coffee shops, airports, or any network you don’t control, a VPN adds a shield around your IMAP traffic.
- Bypassing geo-restrictions or firewall rules: Some workplaces or ISPs block or throttle mail ports. A VPN can help you route traffic through allowed paths, though this is context-dependent.
- Employer or organization policies: Some organizations require VPN use to access corporate mail servers. If that’s your case, following policy is essential.
Data point: global VPN usage has grown significantly in the past few years, with millions of daily users relying on VPNs to protect sensitive traffic beyond just browsing. While exact numbers vary, the trend is clear: more people trust VPNs for securing non-browser traffic, including email.
How IMAP works and where VPN helps
- IMAP basics: IMAP Internet Message Access Protocol lets you access and manage emails on a server. It typically uses ports 143 unsecured or 993 IMAPS, which is SSL/TLS secured.
- What a VPN does: A VPN creates an encrypted tunnel from your device to the VPN server, then accesses the internet from that server. Your local ISP or network only sees encrypted VPN traffic.
- Where VPNs help in IMAP:
- Encrypting client-to-VPN and VPN-to-server paths when you’re on untrusted networks.
- Shielding metadata from local observers note: VPNs don’t magically hide all metadata from the server-side provider or the VPN provider’s own logs.
Key point: If your IMAP server already enforces TLS which it should, a VPN adds another layer of encryption for the path to the VPN server, not a replacement for TLS.
Format tip: Here’s a quick comparison to visualize the layers
- Without VPN: Client <-> TLS IMAPS 993 <-> IMAP server
- With VPN: Client <-> VPN tunnel <-> TLS IMAPS 993 <-> VPN exit <-> IMAP server
- Benefit: Local network privacy + potential bypass of network restrictions; Caution: Potential double encryption overhead can add latency.
When a VPN can be risky for IMAP
- Latency and reliability: VPNs add hops between you and the server. If you’re on a slow connection or the VPN server is congested, you’ll notice delays and possibly timeouts during authentication.
- Split tunneling pitfalls: If you route only some traffic through the VPN split tunneling, misconfigurations can leak IMAP traffic outside the VPN, defeating the purpose.
- DNS leaks: If your VPN isn’t protecting DNS requests, you might reveal the IMAP server hostname to your ISP.
- Authentication issues: Some VPNs can interfere with multi-factor authentication prompts or certificate checks if DNS or routing changes cause mixed-path traffic.
- Logging and privacy: The VPN provider could log activity. If privacy is a concern, choose a provider with a strict no-logs policy and strong jurisdiction.
- Compatibility with corporate policies: In enterprise environments, VPNs might be disallowed or require specific configurations, especially with MDM and device trust policies.
Tip: If you’re using email for critical work, test both with and without VPN on a controlled basis to understand differences in latency and reliability.
VPN features that matter for email
- Strong encryption: AES-256 or better, with modern protocol support OpenVPN, WireGuard, etc..
- DNS leak protection: Ensure the VPN forces all DNS queries through the VPN tunnel.
- Kill switch: Prevents traffic leaks if the VPN drops unexpectedly.
- Split tunneling control: Ability to exclude non-email traffic when needed, but use cautiously.
- Server distribution: A broad set of servers can reduce latency by connecting to a nearby exit node.
- Privacy policy and jurisdiction: Favor providers with transparent policies and strong privacy protections.
- Compatibility with your devices: Windows, macOS, Linux, iOS, Android—all should have reliable clients.
- Threat protection features: Some VPNs offer built-in malware protection or ad-blocking, which can be a nice side benefit.
Step-by-step setup guide
Step 1: Assess your IMAP server and client setup The Best Free VPNs for CapCut Edit Without Limits: Safe, Fast, and Free Options for Pros
- Confirm your IMAP server is accessible over TLS IMAPS on port 993.
- Verify whether your client supports VPN usage without breaking certificate checks.
- Decide if you want full-tunnel or split-tunnel VPN usage for email.
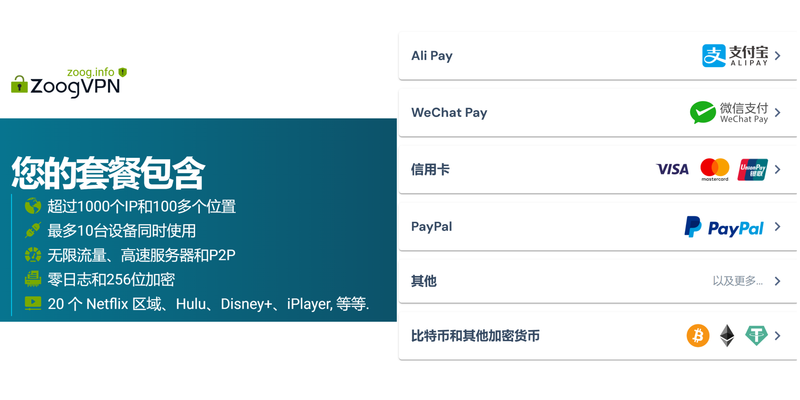
Step 2: Choose a reputable VPN provider
- Look for:
- AES-256 encryption, WireGuard/OpenVPN support
- Strong DNS leak protection and a clear no-logs policy
- A kill switch and reliable mobile apps
- A broad server network and acceptable performance
- Example providers in the market research current offerings to pick one that fits your needs.
Step 3: Install and configure the VPN client
- Install on your device desktop/mobile and sign in.
- Enable DNS leak protection and the kill switch.
- If you’re uncertain about routing all traffic, start with full tunneling to assess impact on IMAP performance.
Step 4: Connect to a VPN server near your IMAP server
- Proximity matters: pick a server geographically close to your mail server to minimize latency.
- Test latency: run ping or traceroute where possible to compare before/after VPN connection.
Step 5: Configure your IMAP client
- Ensure the client is set to use IMAPS port 993 or STARTTLS as appropriate.
- If your VPN is active, verify that TLS certificate checks still pass and there are no DNS leaks for the IMAP server hostname.
- Enable any corporate or personal security features your client supports two-factor prompts, app passcodes, etc..
Step 6: Test mail flow and reliability Cara Mengaktifkan vpn gratis microsoft edge secure network di 2026: Panduan Lengkap, Tips, dan FAQ
- Send and receive multiple messages to ensure there’s no intermittent drop.
- Check for authentication prompts failing or delays during login.
- Monitor for timeouts and verify that the VPN does not drop mid-session.
Step 7: Optimize and monitor
- If you notice increased latency, try a nearby server or adjust split tunneling settings if you’re using it.
- Periodically review VPN logs and client alerts to catch unusual activity.
- Keep your VPN app updated for security patches.
Table: Pros and cons of using a VPN for IMAP
| Pros | Cons |
|---|---|
| Enhanced privacy on untrusted networks | Potential added latency |
| Bypass certain network restrictions | Possible authentication delays |
| Extra layer of protection alongside TLS | Risk of DNS leaks if not configured correctly |
| Helpful in public places like coffee shops | Requires ongoing management of VPN credentials and settings |
Common pitfalls and troubleshooting
- DNS leaks: If your DNS queries leak, your IMAP server hostnames could be exposed. Ensure DNS leak protection is enabled and consider using a VPN with a dedicated DNS service.
- Certificate validation issues: Some VPNs can cause certificate checks to fail if time drift or routing changes occur. Verify system time and certificate trust chain.
- VPN dropouts: If the VPN disconnects, you may briefly lose access to the IMAP server. Use a kill switch to prevent unencrypted exposure.
- Split tunneling misconfigurations: Only route non-email traffic through the VPN, but ensure the IMAP traffic is covered to avoid leaks.
- Incompatible client apps: Some legacy email clients may not handle VPN routing gracefully. Test with your specific client.
- Corporate policy conflicts: If you’re on a managed device, VPN usage might conflict with device management policies. Check with IT.
Troubleshooting quick tips:
- If you can’t connect: try a different VPN server, verify TLS is enforced on the server side, and ensure port 993 is open.
- If you notice slow performance: test without VPN, check VPN server load, and switch to a closer exit node.
- If you get certificate warnings: ensure your system time is correct, and verify that you’re not failing certificate pinning or MITM checks.
Security best practices beyond VPN
- Use TLS everywhere: Ensure IMAP servers require TLS and that clients verify certificates strictly.
- Enable MFA on email accounts and, if possible, app-specific passwords or OAuth2 flows for clients.
- Regularly rotate passwords and use unique credentials for mail servers.
- Keep clients and server software updated with security patches.
- Consider hardware security modules HSMs or modern authentication methods where supported.
- Use separate networks for work and personal devices to limit exposure if a device is compromised.
- Review your VPN provider’s privacy policies and data handling practices.
- Periodically audit access logs on your IMAP server to detect unusual login activity.
Real-world scenarios and decision tips
Scenario A: You travel and use public Wi-Fi to check work email
- Recommendation: Use a VPN with strong DNS leak protection, kill switch, and a fast server near your mail server. This minimizes exposure on public networks and reduces risk of credential interception.
Scenario B: You’re connected from a trusted home network Jiohotstar Not Working With VPN Heres How To Fix It: VPNs, Geoblocks, and Quick Troubleshooting For Streamers
- Recommendation: You can evaluate whether VPN is needed for privacy on that network. If you’re confident in your home network, you might disable the VPN to reduce latency, but keep TLS enabled for client-server communication.
Scenario C: Your corporate IT requires VPN for mail access
- Recommendation: Follow IT policy strictly. Test VPN profiles assigned by IT and ensure compatibility with your mail client and MFA methods.
Scenario D: You notice intermittent IMAP authentication issues when VPN is on
- Recommendation: Try a nearby server, ensure the kill switch is active, and verify that DNS is not leaking hostname data. If problems persist, consult the VPN provider’s support for split-tunneling options.
Scenario E: You’re worried about VPN provider privacy
- Recommendation: Choose a provider with a transparent no-logs policy, audited by third parties, and strong legal frameworks. If possible, opt for providers with independent security assessments.
Frequently Asked Questions
How does a VPN protect IMAP traffic?
A VPN creates an encrypted tunnel between your device and the VPN server, which helps conceal your IMAP traffic from local network observers. This is in addition to the TLS encryption used by IMAP, not a replacement for it.
Can I use a VPN with all IMAP clients?
Most modern IMAP clients support VPN usage, but some older or highly customized clients may behave differently. Always test your specific client to ensure authentication, TLS checks, and server connections work as expected. Why Your VPN ISNT Working With Paramount Plus And How To Fix It: VPNs, Geo-Blocking, And Streaming Gotchas
Will a VPN slow down my email speed?
Yes, potentially. VPNs add extra routing and encryption overhead. The impact depends on VPN server location, network congestion, and your own connection speed. If latency becomes an issue, try a nearby server or adjust VPN settings.
Should I use split tunneling for IMAP?
Split tunneling can be helpful to route only email traffic through the VPN, but it introduces risks of traffic leaks. Use it only if you understand the routing rules and keep ransomware/malware protection enabled on all paths.
How do I prevent DNS leaks with a VPN on IMAP?
Enable DNS leak protection in your VPN client, use a VPN that forces DNS through the tunnel, and consider using an independent DNS service that respects privacy.
Is it safer to access IMAP on public networks with a VPN?
Yes, a VPN adds a layer of protection on untrusted networks. However, ensure TLS is still enforced on the IMAP server and that your VPN is trustworthy and correctly configured.
Do VPNs hide my email content from the email provider?
A VPN hides traffic from your local network and intercepting observers. Your provider can still read metadata and the content if they have access to the encrypted payload, unless end-to-end encryption or other protections are used. TLS protects data in transit to the IMAP server. The Ultimate Guide to Setting Up a VPN on Your Cudy Router
Can VPNs interfere with two-factor authentication?
They can, especially if the VPN causes IP or geolocation inconsistencies. If you use MFA, be prepared for prompts, and ensure your backup methods are available.
What are the signs of a VPN-related IMAP issue?
Look for increased latency, frequent timeouts during authentication, certificate warnings, DNS resolution problems, or sudden changes in IP addresses assigned by the VPN.
Should I always use a VPN for IMAP?
Not always. If you’re on a trusted network, using TLS with strong credentials may be sufficient. Consider VPN benefits for public or untrusted networks, then weigh latency and reliability trade-offs.
How often should I review VPN settings for IMAP?
Periodically review server proximity, VPN server load, DNS protection settings, and the provider’s privacy policy—at least every few months or after a major network or provider update.
Are there alternatives to VPN for securing IMAP?
Yes. VPNs aren’t the only option. You can use TLS with strong client certificates, integrate with SSH tunnels in some setups, or rely on enterprise-grade email security gateways and zero-trust solutions. Unifi and nordvpn your ultimate guide to secure networking: Mastering VPNs, UniFi, and smart online security
Can I use a VPN to access multiple email accounts at once?
Yes, as long as your VPN connection remains stable and you configure each client correctly. Monitor performance if you’ve got several accounts active simultaneously.
What about home servers or self-hosted IMAP?
If you self-host, a VPN can help protect access to your server from untrusted networks. Ensure you implement TLS, robust authentication, and firewall rules to restrict access.
Do VPNs keep logs of my IMAP activity?
That depends on the provider. Look for a clear no-logs policy, third-party audits, and a jurisdiction that respects privacy. Always read the privacy policy before committing.
Can I rely on a free VPN for IMAP security?
Free VPNs often come with limitations like data caps, slower speeds, and questionable privacy practices. For sensitive email, choose a trusted paid service with a strong privacy stance.
If you found this guide useful and want a reliable way to secure your email on the go, check out NordVPN for extra protection affiliate link: – https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441 Nordvpn Price In India: Budget VPNs, Plans, And Smart Tips To Save
Sources:
Vpn china server 中国服务器 VPN 使用指南:在中国环境下选择、配置与优化
Vpn软件下载:选择、使用与常见问题全攻略,提升隐私与访问自由
翻墙机场 ⭐ clash:新手入门指南与实用技巧
谷歌VPN:全面指南、实用比较与最新趋势
Vpn をオフにする方法:デバイス別の完全ガイド(2026 Top des vpn gratuits pour boitier android tv et purevpn en 2026